Welcome to the blog! For those looking to dive into one of the fastest-growing and most critical fields in the world, this is where your journey begins. Cybersecurity is a dynamic, challenging, and incredibly rewarding domain, and the world is desperate for skilled defenders.
This post will serve as your first map. We’ll break down the basic concepts, the foundational knowledge you need, the different career paths you can choose, and how to get your hands dirty in a safe, legal environment.
What is Cybersecurity? The Core Concepts
At its heart, cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. It’s not just about protecting data; it’s about ensuring businesses can operate, hospitals can treat patients, and people can communicate securely.
These attacks aren’t just from lone “hackers” in basements. They come from organized crime syndicates, state-sponsored groups, and malicious insiders. Our modern world, built on interconnected data, cloud computing, and Internet of Things (IoT) devices, has a massive “attack surface.” Our job is to defend it.
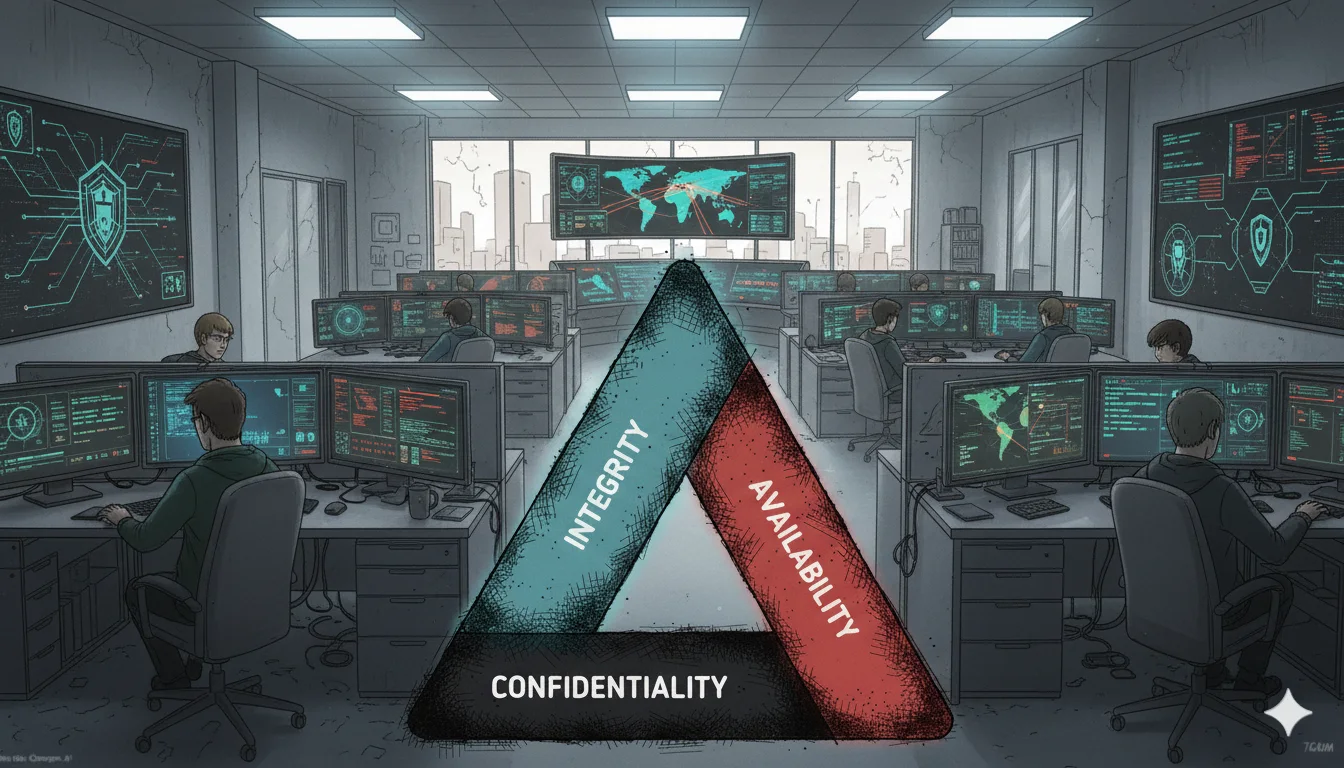
Key Concepts: The CIA Triad
Every security measure, policy, and control is designed to support these three goals:
- Confidentiality: Keeping secrets private. This means ensuring that data is accessible only by authorized individuals. We achieve this through Encryption (scrambling data so it’s unreadable without a key), Access Controls (ACLs), and strong authentication.
- Integrity: Ensuring data is trustworthy. This means verifying that data is accurate, complete, and has not been tampered with or corrupted (either maliciously or accidentally). We achieve this using Hashing (creating a unique digital “fingerprint” for data) and digital signatures.
- Availability: Ensuring systems are operational. This means making sure that authorized users can access the information and systems when they need them. This is defended against attacks like Denial of Service (DoS) and supported by Backups, Redundancy (e.g., backup power, redundant servers), and disaster recovery plans.
Beyond the Triad, you’ll hear these terms constantly:
- Authentication (AuthN): Proving you are who you say you are. This is “Phase 1.” Examples include passwords, biometrics (fingerprints), or a multi-factor authentication (MFA) app.
- Authorization (AuthZ): Determining what you are allowed to do once you’re authenticated. This is “Phase 2.” Just because you can log in to the system (Authentication) doesn’t mean you should be able to read the HR files (Authorization).
- Non-Repudiation: Ensuring that someone cannot deny having taken an action. Think of a signed contract or a secure log entry. Digital signatures and audit trails provide non-repudiation, which is critical for legal and financial transactions.
Risk Management: The Language of the Business
Cybersecurity professionals spend their careers managing and mitigating risk. These terms are the foundation of that work:
- Asset: The “thing” you are trying to protect (e.g., data, a server, a laptop, company reputation).
- Threat: A potential danger that could harm an asset (e.g., a cybercriminal, a natural disaster, a disgruntled employee).
- Vulnerability: A weakness in a system or design that a threat can exploit (e.g., unpatched software, a weak password, an unlocked door).
- Exploit: The specific tool or technique used by a threat to take advantage of a vulnerability.
- Risk: The potential for loss or damage when a threat successfully exploits a vulnerability. We calculate this as Risk = Threat x Vulnerability. Our job is to reduce risk to an acceptable level, often by applying a Control or Mitigation (like installing a firewall, enforcing MFA, or training employees).
What You Need to Learn: The Technical Foundation
You cannot secure what you do not understand. Before you specialize, you need a broad technical foundation. Focus on mastering these areas first:
Networking
Networking is the language of the internet and the most vital foundational skill.
- The Models: Understand both the TCP/IP Model (the practical model) and the OSI Model (the theoretical model). Knowing the “layers” (e.g., Physical, Data Link, Network, Transport) helps you understand where different attacks and defenses live.
- IP Addressing & Subnetting: Learn how networks are logically organized and how devices find each other.
- Core Protocols: Know the function of HTTP/HTTPS (web), DNS (the internet’s phonebook), DHCP (assigning IPs), SMTP (email), and SSH/RDP (remote access).
- Network Security Concepts: Understand the purpose of a Firewall (a digital bouncer), a VPN (a secure tunnel), and a Proxy (a middle-man).
- Command-Line Tools: Get comfortable with ping (is it on?), traceroute/tracert (what path does my data take?), ipconfig/ifconfig (what’s my address?), and netstat (what connections are active?).
Operating Systems
You need to know how computers fundamentally operate to secure them.
- Linux: This is non-negotiable for most security roles. It runs the internet’s servers, cloud platforms, and most security tools. Master the Bash command line, file permissions (chmod, chown), package management, and service administration.
- Windows: The dominant force in corporate environments. Understand Active Directory (AD) (the identity and access hub for most companies), PowerShell (for administration and scripting), the Windows Registry, and common system administration features.
- macOS: Increasingly common in creative and tech-focused businesses, it’s a Unix-based OS with its own unique security quirks.
- Virtualization: Learn to use VirtualBox or VMware Workstation Player to create isolated lab environments. This is essential for safe practice.
Coding/Scripting
You don’t need to be a software engineer, but scripting skills are a superpower. They allow you to automate security tasks, analyze data, and understand how attacks work.
- Python: The undisputed king of security scripting. It’s used for automation, malware analysis, building tools, and data analysis.
- Bash/PowerShell: Essential for administration and “living off the land” (using a system’s built-in tools) on Linux and Windows systems, respectively.
- SQL (Structured Query Language): The language of databases. Understanding how to query a database is the first step to understanding (and preventing) SQL Injection, one of the most devastating web vulnerabilities.

Choosing Your Cybersecurity Niche
Cybersecurity is a massive industry with roles for every skill set. As a beginner, it helps to understand the main “teams” and job types.
The Defensive Teams (Blue Team)
These roles focus on protecting assets, monitoring for threats, and responding to incidents. They are the first line of defense.
- Security Analyst (SOC Analyst): The “guard on the wall.” You monitor security logs using a SIEM (Security Information and Event Management) tool like Splunk or Sentinel, looking for signs of an attack (e.g., “Alert! 500 failed logins from a weird IP!”).
- Incident Responder: The “firefighter.” When a breach does happen, you are called in to stop the attack, assess the damage, and get the systems back online securely.
The Offensive Teams (Red Team)
These roles simulate real-world attacks to identify and fix weaknesses before criminals exploit them. They require a “breaker” mindset and deep technical knowledge.
- Penetration Tester: Hired to legally “break into” a specific system, network, or application to find vulnerabilities. You then write a detailed report on how you got in and how to fix it.
- Vulnerability Assessor: Runs automated scanning tools to find “low-hanging fruit” and known vulnerabilities, then helps prioritize them for patching.
The Building & Architecture Teams
These roles embed security into systems from the ground up, making development and infrastructure inherently safe.
- Security Engineer: Designs, builds, and maintains the company’s security infrastructure (firewalls, VPNs, authentication systems).
- Cloud Security Engineer/Architect: Specializes in securing cloud platforms like AWS, Azure, or Google Cloud (GCP). This is a high-demand, high-growth area.
- Application Security (AppSec) Engineer: Works with software developers to find and fix security flaws in code before it’s released. They use tools for SAST (Static Analysis, “reading” the code) and DAST (Dynamic Analysis, “attacking” the running app).
The Forensics & Intelligence Teams
These are highly specialized roles for those who love deep investigation.
- Digital Forensics (DFIR) Analyst: The “crime scene investigator.” After a breach, they meticulously recover data from hard drives, phones, and memory to piece together exactly what an attacker did.
- Threat Intelligence Analyst: The “spy.” You study who the attackers are (e.g., a specific Russian ransomware gang), what their motives are, and what tools and tactics (TTPs) they use. You provide this “intelligence” to the Blue Team so they know what to look for.
The Audit and Policy Teams (GRC)
These roles deal less with keyboard commands and more with documents, laws, and policies. This is a fantastic path for organized, detail-oriented people.
- Security Auditor: Assesses an organization’s security against an established set of rules or frameworks (like NIST, ISO 27001, or PCI-DSS for credit cards).
- GRC Analyst (Governance, Risk, Compliance): The “glue” that connects the technical side (IT/Security) to the business side (Legal/Execs). They create security policies, manage risk registers, and ensure the organization follows legal requirements (like GDPR, HIPAA, or CCPA).
Starting Your Practice: The Home Lab Environment
You must practice, but you must do so safely and legally. Never practice hacking or scanning on systems you do not own or have explicit permission to test.
Building Your Virtual Lab
Use virtualization software (like VirtualBox or VMware Workstation Player) to create an isolated “lab” on your own computer. This allows you to safely set up and break things without harming your main operating system.
- Install an Attacker Machine: Kali Linux is the standard. It comes pre-loaded with hundreds of security tools.
- Install a Target Machine: Install a “deliberately vulnerable” image like Metasploitable or OWASP Juice Shop (for web hacking). You can also install a plain Windows Server or Linux instance to practice hardening and defending it.
Using Online Training Grounds
Websites dedicated to security learning provide legal, guided, and gamified environments:
- TryHackMe: The best starting point. It offers “Rooms” that are step-by-step learning paths, guiding you through concepts and tools.
- Hack The Box (HTB): The next step up. It features retired “Boxes” (vulnerable machines) that are more challenging and require less hand-holding.
- Capture The Flag (CTFs): Participate in these competitions (see sites like CTFtime.org) to solve security-related puzzles and build problem-solving skills in a competitive environment.

How to Learn: Focused Tips for Success
- Document Everything: As you learn a new command or compromise a box in your lab, write it down. Use a note-taking app (Notion or Obsidian) as your personal knowledge base. This will become your “second brain” and is invaluable for interviews.
- Get Involved: Join the community. Participate in subreddits like r/cybersecurity, r/netsecstudents, or r/SecurityCareer. Listen to security podcasts. Find a Discord server. The community is famously helpful to newcomers.
- Read the News: Follow sites like The Hacker News. This teaches you how real-world breaches happen and keeps you current.
- Be Curious, Not Overwhelmed: You will encounter a firehose of information. You cannot learn it all at once. Pick one thing (e.g., the Nmap tool), learn it deeply, practice it, and then move to the next thing. Consistency beats intensity.